style="background-image:url(https://rickwilliamsleadership.com/wp-content/uploads/2024/02/banner.jpg);"
Rick Williams
Helping Leaders Succeed
Board Member | Speaker |
Thought Leader | Author
Rick Williams—a deeply experienced corporate leader, management consultant, company founder, and board member.
His board of directors’ service builds on his belief that boards can be value accelerators for their company.
An engaging speaker with a message of hope and inspiration. “We create the future by the choices we make, by the decisions we make.”

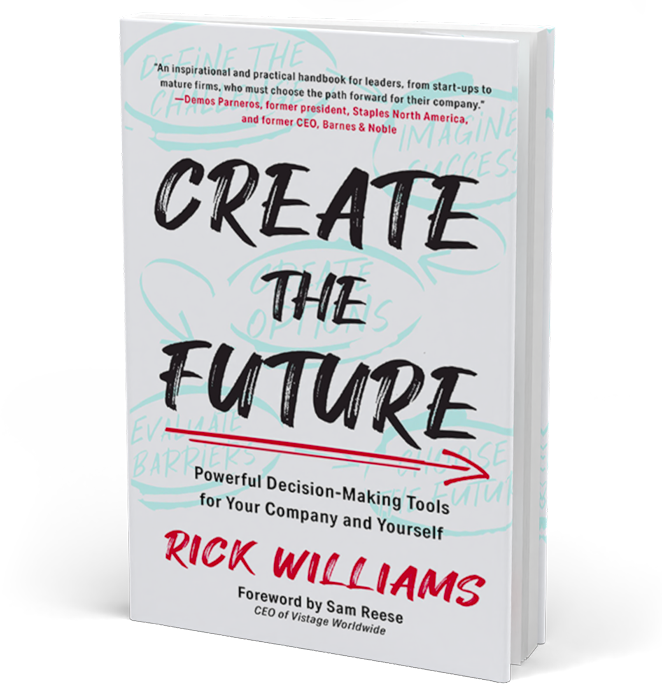
“An inspirational and practical handbook for leaders, from start-ups to mature firms, who must choose the path forward for their company.”
Demos Parneros, former president, Staples North America, and former CEO, Barnes & Noble
“Like an in-house management consultant, Create the Future is your invaluable resource for decision-making in turbulent times.”
Hubert Joly, Former Best Buy CEO, senior lecturer Harvard Business School, Author The Heart of Business
Foreword written by Sam Reese, CEO of Vistage Worldwide
Speaking
Rick speaks about impactful leadership drawing on his CEO, board, and corporate advisor experience. Topics include creating the future by making better decisions for your company and yourself, imagining success, and maximizing the value of your board of directors.

Board of Directors
Rick Williams serves on the board directors of technology companies in the Business to Business space. He is a nationally recognized authority on how to maximize value from your board and serves on the national board of directors of the Private Directors Association, PDA.
Rick’s Blog
Read Rick’s thoughts on business trends, current events, and evergreen lessons for leaders.

Right and Wrong – Your Leadership Imperative
Rick’s Articles
Explore Rick’s nationally and internationally published articles.
Firing the CEO - Board Lessons from OpenAI and Harvard
Maximizing the Value From Your Board of Directors
Raising Equity Capital – Getting Started
Rick’s Newsletter
A newsletter with a CEO and Board of Directors’ point of view—get this blog in your inbox:
“I’d say your newsletter is the very best that I receive, and I receive a lot of them!”
Mark Newhall, CEO, Execution Specialists Group LLC
“Thank you Rick for your clarity in this article. It will help me talk about this issue more clearly and confidently.”
Scott Thurber, Vistage CEO Peer Group Chair
By submitting this form, you are consenting to receive marketing emails from: Rick Williams. You can revoke your consent to receive emails at any time by using the SafeUnsubscribe® link, found at the bottom of every email. Emails are serviced by Constant Contact